Social engineering scams have been going on for years, however, they are getting more and more sophisticated which makes them harder to detect.
Here’s a quick and dirty summary of today’s most common and deadly social engineering scams provided with insight from our friends at BOXX Insurance, the cyber insurance specialists. After all, if everyone learns to identify these attacks, avoiding them will be much easier than being offline for days!
Phishing: Phishing is the most common form of social engineering attacks that are typically delivered in the form of an email, chat, web ad or website that has been designed to impersonate a real organization. Phishing messages are crafted to deliver a sense of urgency or fear with the end goal of capturing an end user’s sensitive data. A phishing message might appear to come from a bank, the government or a major corporation. The call to actions vary. Some ask the end user to “verify” their login information of an account, and include a mocked-up login page complete with logos and branding to look legitimate.
Baiting: Baiting involves offering something enticing to an end user, in exchange for login information or private data. The “bait” comes in many forms, both digital, such as a music or movie download on a peer-to-peer site, and physical, such as a corporate branded flash drive labeled “Executive Salaries Q3 2018” that is left out on a desk for an end user to find. Once the bait is downloaded or used, malicious software is delivered directly into the end user’s system and the hacker is able to get to work.
Quid Pro Quo: Quid pro quo involves a hacker requesting the exchange of critical data or login credentials in exchange for a service. For example, an end user might receive a phone call from the hacker who, posed as a technology expert, offers free IT assistance or technology improvements in exchange for login credentials. Another common example is a hacker, posed as a researcher, asks for access to the company’s network as part of an experiment in exchange for $100. If an offer sounds too good to be true, it probably is quid pro quo.
Pretexting: Pretexting, the human equivalent of phishing, is when a hacker creates a false sense of trust between themselves and the end user by impersonating a co-worker or a figure of authority well known to an end user in order to gain access to login information. An example of this type of scam is an email to an employee from what appears to be the I.T Helpdesk manager.
Piggybacking: Piggybacking, also called tailgating, is when an unauthorised person physically follows an authorised person into a restricted corporate area or system. One tried-and-true method of piggybacking is when a hacker calls out to an employee to hold a door open for them as they’ve forgotten their ID card. Another method involves a person asking an employee to “borrow” his or her laptop for a few minutes, during which the criminal is able to quickly install malicious software.
For all employees to be aware of the various forms of social engineering is essential to reduce the risk of a social engineering attack. If end users know the main characteristics of these attacks, it’s much more likely they can avoid falling for them.
What else should we do?
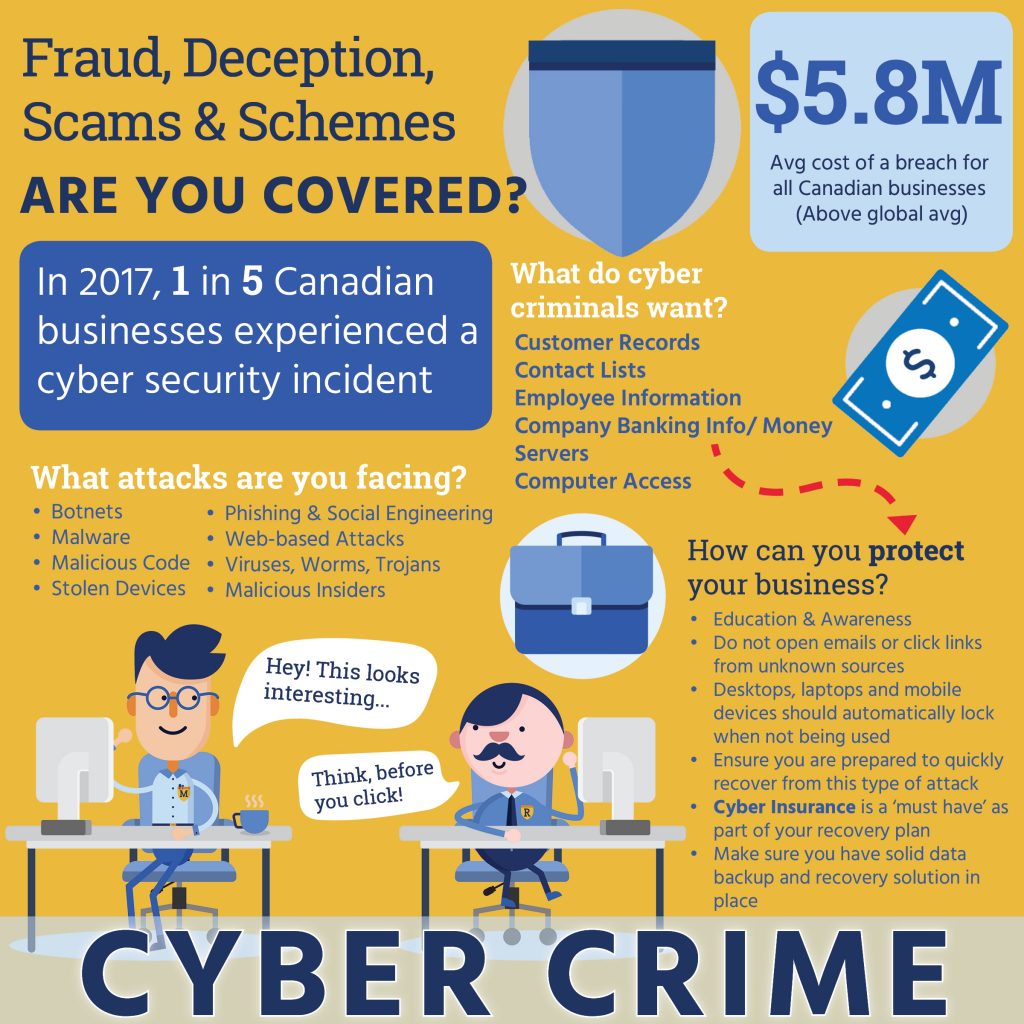
Aside from education and awareness, there are further actions you can take to reduce the risk of being hacked.
- Employees should be instructed not to open emails or click links from unknown sources. Computers should never be shared with anyone.
- By default, all company desktops, laptops and mobile devices should automatically lock when left idle.
- Ensure your business is prepared to quickly recover from this kind of attack. Humans are humans after all. Cyber insurance is a ‘must have’ component of your disaster recovery plan.
- Finally, make sure you have a solid data backup and recovery solution in place.
Learn more about how you can help your business stay ahead of cyber threats with McFarlan Rowlands.